
Cybersecurity corporate Imperva on Friday mentioned it not too long ago mitigated a ransom dispensed denial-of-service (DDoS) assault concentrated on an unnamed site that peaked at 2.5 million requests according to 2d (RPS).
“Whilst ransom DDoS assaults don’t seem to be new, they seem like evolving and changing into extra attention-grabbing with time and with every new section,” Nelli Klepfish, safety analyst at Imperva, mentioned. “As an example, we now have observed circumstances the place the ransom word is integrated within the assault itself embedded right into a URL request.”
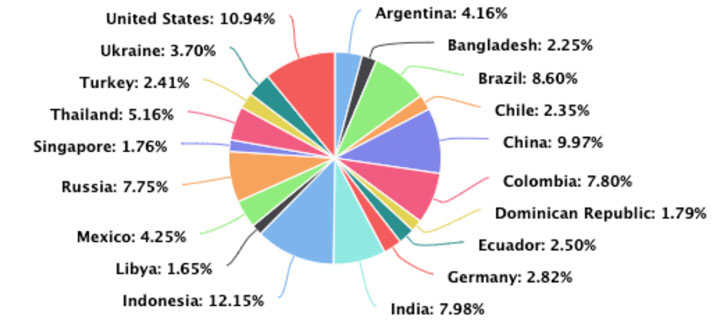
The highest assets of the assaults got here from Indonesia, adopted by means of the U.S., China, Brazil, India, Colombia, Russia, Thailand, Mexico, and Argentina.
Dispensed denial-of-service (DDoS) assaults are a subcategory of denial-of-service (DoS) assaults during which a military of attached on-line gadgets, referred to as a botnet, is used to weigh down a goal site with faux site visitors in an try to render it unavailable to official customers.
The California-headquartered company mentioned that the affected entity won more than one ransom notes integrated as a part of the DDoS assaults, difficult the corporate make a bitcoin fee to stick on-line and steer clear of dropping “loads of hundreds of thousands in marketplace cap.”
In a fascinating twist, the attackers are calling themselves REvil, the notorious ransomware-as-a-service cartel that suffered a big setback after numerous its operators had been arrested by means of Russian regulation enforcement government previous this January.
“It isn’t transparent alternatively whether or not the threats had been truly made by means of the unique REvil staff or by means of an imposter,” Klepfish famous.
 |
| Assault origins |
The two.5 million RPS assault is alleged to have lasted not up to a minute, with some of the sister websites operated by means of the similar corporate maintaining a identical assault that lasted roughly 10 mins, even because the techniques hired had been continuously modified to avert conceivable mitigation.
Proof collected by means of Imperva issues to the DDoS assaults originating from the Mēris botnet, which has persisted to leverage a now-addressed safety vulnerability in Mikrotik routers (CVE-2018-14847) to strike objectives, together with Yandex closing September.
“The forms of websites the danger actors are after seem to be industry websites that specialize in gross sales and communications,” Klepfish mentioned. “Goals have a tendency to be U.S.- or Europe-based with the only factor all of them have in not unusual being that they’re all exchange-listed corporations and the danger actors use this to their merit by means of relating to the prospective harm a DDoS assault may just do to the corporate inventory value.”
Learn how to Prevent Ransomware with Actual-Time Coverage
Sign up for our webinar and learn to prevent ransomware assaults of their tracks with real-time MFA and repair account coverage.
The findings come as malicious actors had been noticed weaponizing a brand new amplification methodology referred to as TCP Middlebox Mirrored image for the first actual time within the wild to hit banking, shuttle, gaming, media, and internet webhosting industries with a flood of pretend site visitors.
The ransom DDoS assault may be the second one botnet-related task avoided by means of Imperva because the get started of the yr, what with the corporate detailing a internet scraping assault that focused an unidentified process checklist platform in overdue January.
“The attacker used a large-scale botnet, producing at least 400 million bot requests from just about 400,000 distinctive IP addresses over 4 days with the intent of harvesting process seekers’ profiles,” the protection company mentioned.
Supply By means of https://thehackernews.com/2022/03/imperva-thwarts-25-million-rps-ransom.html


